A software bill of materials (SBOM) for containers and AI code is a machine-readable inventory of all components, versions, and licenses in an image or repo. In 2026, effective supply chain security combines automated SBOM generation and attestation in CI with behavior-based scanning to catch malicious or risky code that SBOM metadata alone cannot reveal.
What is an SBOM in the Context of Containers and AI Code?
An SBOM (Software Bill of Materials) is a formal record detailing every component in your software supply chain. For containers, this includes all layers, packages, and libraries within a Docker or OCI image. For AI code, it extends to dependencies like Python packages from PyPI, JavaScript modules from npm, and AI model files or MCP server components.
According to the US Executive Order 14028 and subsequent guidance, SBOMs are becoming a baseline requirement for software suppliers, driving adoption across industries. This transparency enables you to track vulnerabilities, manage licenses, and respond swiftly to incidents like Log4Shell.
In AI development, where agents frequently pull code from various sources, an SBOM is critical. It provides visibility into what's inside your AI application's supply chain, helping you mitigate risks hidden in dependencies before deployment.
Which SBOM Formats Should You Use for Containers and AI Applications?
The two dominant SBOM formats are SPDX (Software Package Data Exchange) and CycloneDX. SPDX, maintained by the Linux Foundation, is an ISO standard focused on license compliance and component identification. CycloneDX, from OWASP, emphasizes security use cases like vulnerability reporting and is designed for CI/CD integration.
According to the SEI blog on SBOM quality, choosing the right format depends on your primary goal: SPDX for comprehensive legal compliance, CycloneDX for agile security workflows. For containers and AI code, CycloneDX's JSON schema is often preferred due to its DevOps tool integration, but SPDX is essential for regulatory requirements.
Other formats like SWID tags exist but are less common for cloud-native applications. Consider tool support, community adoption, and compliance needs when selecting a format.
SBOM Format Comparison: SPDX vs CycloneDX
How Do You Generate SBOMs for Container Images and Repositories?
| Feature | SPDX | CycloneDX |
|---|---|---|
| Standardization | ISO/IEC 5962:2021 Standard | OWASP Community Standard |
| Primary Focus | License Compliance & Component Tracking | Security & Vulnerability Management |
| Common Use Case | Regulatory Compliance, Audits | CI/CD Integration, DevOps |
| Output Formats | RDF, JSON, YAML, Tag/Value | JSON, XML |
| Tool Support | Wide in enterprise ecosystems | Strong in DevOps and security tools |
Generating SBOMs can be done manually or with automated tools. For container images, use CLI tools like Syft or Trivy. For example, syft docker:image-name produces an SBOM in SPDX or CycloneDX format. For AI code repositories, tools like npm audit or pip-audit can generate dependency lists, but dedicated SBOM generators like cyclonedx-bom are more comprehensive.
Step-by-step approach:
-
For Containers: Run a scanner on your Docker image to list all packages. Syft is popular for its speed and multi-format support.
-
For AI Repos: Analyze your
package.json,requirements.txt, or other manifest files to extract dependencies. Integrate this into your build process. -
Combine Sources: If your AI application uses both containers and external packages, merge SBOMs to create a complete view.
Automation is key to maintaining accurate SBOMs as your code evolves. Research from JISIS on SBOM generation effectiveness shows that automated pipelines reduce errors and improve consistency.
For a practical demonstration, watch this tutorial from Bytesafe on generating an SBOM from a Docker container.
How Do You Automate SBOM Generation and Attestation in CI/CD Pipelines?
Automating SBOM generation ensures every build produces an up-to-date inventory. Integrate SBOM tools into your CI/CD pipeline using GitHub Actions, GitLab CI, or Jenkins. For instance, add a step that runs Syft on the container image after build and attaches the SBOM as an artifact.
SBOM attestation involves signing the SBOM with a cryptographic key to verify its authenticity and integrity, crucial for preventing tampering. Use tools like Sigstore's Cosign to attest SBOMs and store them in registries alongside your images.
According to the AWS blog on using SBOMs for vulnerable containers, automation reduces the time to respond to vulnerabilities by providing immediate visibility. Implement attestation to meet compliance requirements and build trust in your software artifacts. This aligns with recommendations for improving SBOM quality through automated, signed workflows.
What Are the Limitations of SBOMs for Detecting Malicious Behavior?
SBOMs excel at inventory management but have critical gaps. They list what components are present, but they cannot analyze what those components do. For example, an SBOM won't flag a dependency containing obfuscated code, malicious install hooks, or data exfiltration routines.
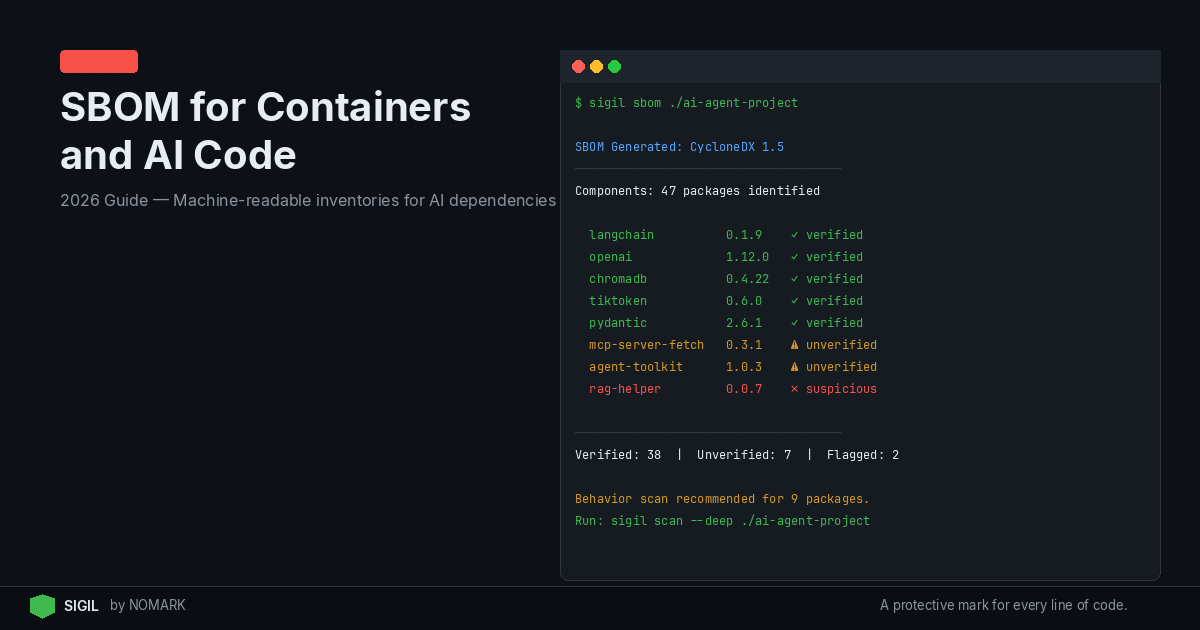
Data indicates that most SBOM implementations today focus on dependency visibility, not on detecting malicious behavior in code. This is where behavior-based scanning tools like Sigil come in. Sigil analyzes code for risky patterns, network calls, and obfuscation before execution, complementing SBOMs.
Relying solely on SBOMs leaves you vulnerable to attacks that exploit legitimate packages with malicious behavior. Combine SBOMs with pre-execution scanning for comprehensive protection against supply chain threats that metadata alone cannot reveal.
How Do SBOMs Complement Behavior-Based Scanning and CVE Tools?
A layered security approach uses SBOMs for visibility, CVE scanners like Snyk or Dependabot for known vulnerabilities, and behavior-based scanners like Sigil for unknown threats. SBOMs provide the ingredient list; CVE tools check for known flaws in those ingredients; and behavior-based tools inspect how the ingredients behave when mixed.
For instance, an SBOM might reveal a vulnerable library version, a CVE scanner would flag it, but only a behavior-based scanner could detect if that library is being used maliciously post-installation. 2026 studies reveal that combining SBOMs with behavioral scanning significantly improves supply chain risk detection.
Integrate these tools into your workflow: generate SBOMs automatically, scan for CVEs, and use Sigil to quarantine and audit AI code before execution. This multi-faceted strategy is essential for modern AI development, addressing both known vulnerabilities and hidden behavioral risks.
What is an SBOM and why is it important for container security?
An SBOM is a machine-readable inventory of all software components in a container image. It's crucial for container security because it provides transparency, enabling vulnerability management, license compliance, and rapid response to supply chain attacks like Log4Shell. Without an SBOM, you lack visibility into what's running in your containers.
Which SBOM formats should I use for containers and AI applications?
For containers and AI applications, the two main formats are SPDX and CycloneDX. SPDX is best for regulatory compliance and license tracking, while CycloneDX is optimized for security integration in CI/CD pipelines. Choose based on your primary use case: compliance mandates often require SPDX, while DevOps teams favor CycloneDX for its lightweight JSON output.
How do I automate SBOM generation and attestation in CI/CD pipelines?
Automate SBOM generation by integrating tools like Syft or Trivy into your CI/CD steps, such as GitHub Actions or GitLab CI. For attestation, use Sigstore's Cosign to sign SBOMs cryptographically, ensuring their authenticity. This creates a verifiable chain of custody for your software artifacts, meeting modern supply chain security standards.
Does an SBOM detect malware or only list dependencies?
An SBOM only lists dependencies and does not detect malware. It provides visibility into components but cannot analyze code behavior. To detect malicious code, you need behavior-based scanning tools like Sigil that inspect for obfuscation, network calls, and other risky patterns before execution. SBOMs are a foundation, not a complete security solution.
How do SBOMs fit with behavior-based scanning tools like Sigil and CVE scanners?
SBOMs, behavior-based scanners, and CVE scanners work together in a layered defense. SBOMs inventory components, CVE scanners flag known vulnerabilities in those components, and behavior-based tools like Sigil detect unknown threats by analyzing code behavior pre-execution. This combination offers comprehensive supply chain security for containers and AI code.
Key Takeaways
-
SBOMs are machine-readable inventories essential for container and AI code transparency, mandated by trends like US Executive Order 14028.
-
Automated SBOM generation and attestation in CI/CD pipelines reduce vulnerability response times and improve auditability.
-
SPDX and CycloneDX are the dominant SBOM formats, with SPDX for compliance and CycloneDX for DevOps security integration.
-
SBOMs alone cannot detect malicious behavior; they must be combined with behavior-based scanning like Sigil for pre-execution risk analysis.
-
Integrating SBOMs with CVE scanners and tools like Sigil provides layered security, addressing both known vulnerabilities and hidden threats in AI supply chains.