Enterprise code quarantine solutions isolate repositories, packages, and artifacts before they run, applying malware, behavior, and vulnerability scans in CI/CD. In 2026, teams typically pair SCA tools like Snyk, Nexus IQ, or JFrog Xray with a pre-execution quarantine layer such as Sigil to block malicious installs, enforce policy, and keep risky AI tooling off developer machines.
Best Enterprise Code Quarantine Solutions in 2026
When evaluating solutions, consider how they integrate into developer workflows, enforce policy, and block threats before execution. Here are the top tools:
-
Sigil: Open-source CLI for pre-execution quarantine with behavior-focused scanning for AI agents and MCP servers.
-
Snyk: Comprehensive SCA and vulnerability management, best for post-install scanning of known CVEs.
-
Sonatype Nexus IQ: Policy-driven SCA and repository firewall for centralized governance.
-
JFrog Xray: Deep recursive scanning integrated with the JFrog Platform for binaries and artifacts.
-
Checkmarx: SAST-focused platform with software supply chain security capabilities.
According to recent DevSecOps surveys, most enterprises now consume thousands of third-party packages across npm, PyPI, and internal registries, making pre-execution gates critical.
What is enterprise code quarantine?
Enterprise code quarantine is a security practice that isolates and inspects code, packages, and artifacts before they are allowed to execute in development, CI/CD, or production environments. It acts as a controlled checkpoint, similar to a network quarantine zone, where automated scans for malware, vulnerabilities, policy violations, and malicious behavior are performed.
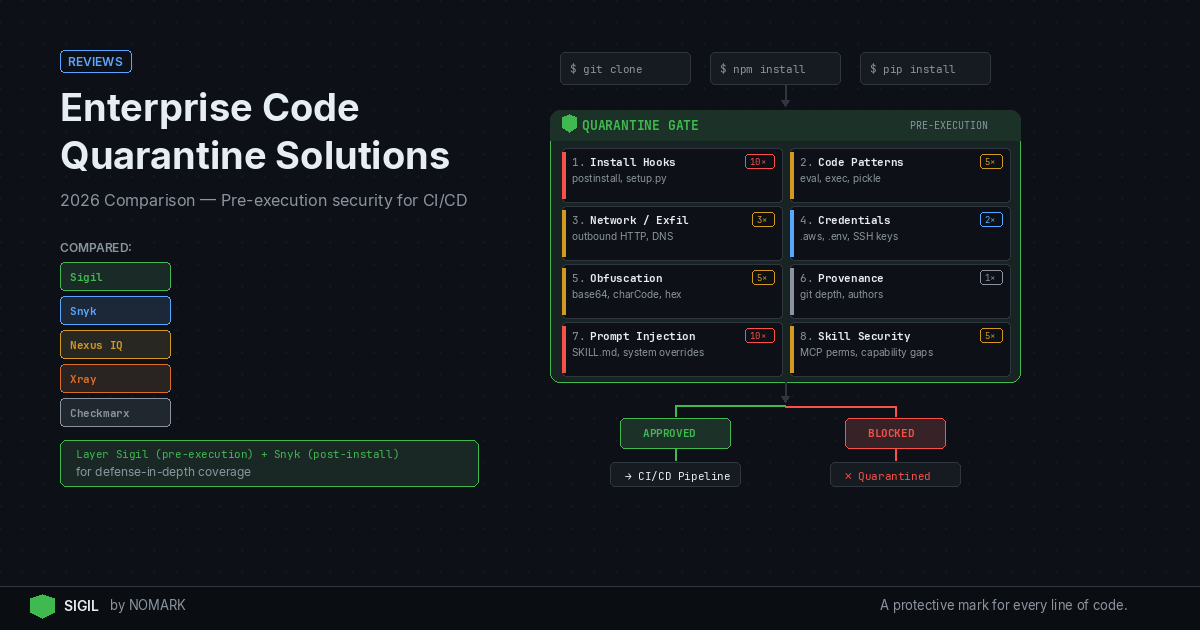
Unlike traditional Software Composition Analysis (SCA) that scans code already in your environment, a quarantine solution intercepts downloads at the source. This includes git clone, npm install, pip install, and artifact pulls from registries. The goal is to stop threats-like hidden install hooks, obfuscated payloads, or credential exfiltration scripts-before they ever run on a developer's machine or in a pipeline. Research shows that many software supply chain attacks succeed before traditional vulnerability scanners have signatures or CVEs available.
Why quarantine before CI/CD and production deployment?
Introducing a quarantine gate significantly reduces the blast radius of a compromised package. Once malicious code executes in your CI/CD pipeline, it can access secrets, poison build artifacts, and deploy backdoors. A pre-execution quarantine provides several key advantages:
-
Blocks Zero-Day Behavior: Catches malware and suspicious activities that lack a CVE, such as encoded
eval()statements or unexpected network calls. -
Enforces Policy Early: Ensures all code meets organizational security policies before it enters the software development lifecycle.
-
Improves Developer Experience: Gives developers immediate, clear risk feedback (e.g., "blocked" or "approved") within their existing CLI workflow, preventing context-switching to a separate security dashboard.
-
Supports Regulatory Compliance: Provides an audit trail proving code was scanned and cleared before use, which is increasingly required by frameworks and regulations. Data indicates that introducing a quarantine gate before deployment is a foundational control in modern application security programs.
Key features of enterprise quarantine solutions
When evaluating code quarantine tools in 2026, look for these essential capabilities:
-
Pre-Execution Interception: The tool must seamlessly replace or hook into package manager commands (
clone,install) to intercept code before it runs. -
Multi-Language & Registry Support: Coverage for npm, PyPI, Go modules, Docker images, MCP servers, and internal artifact repositories.
-
Behavioral Analysis: Detection of risky runtime behaviors like network exfiltration, filesystem access, and credential harvesting-not just static pattern matching.
-
Fast, Local Scans: Analysis must complete in seconds to avoid disrupting developer productivity, ideally working fully offline.
-
Policy Engine & Enforcement: Ability to define custom security policies (e.g., "block packages with postinstall hooks") and automate approvals or denials.
-
CI/CD & Air-Gapped Integration: Native plugins for GitHub Actions, GitLab CI, Jenkins, and support for air-gapped/offline deployments.
-
Comprehensive Audit Logging: Detailed records of all scan results, policy decisions, and user actions for compliance and forensics.
Snyk vs Nexus IQ vs JFrog Xray vs Checkmarx vs Sigil: Comparison
This feature-by-feature comparison highlights how leading SCA and quarantine solutions address the pre-execution security challenge. The key differentiator is when scanning occurs and what types of threats are detected.
Enterprise Code Quarantine & Scanning Solutions Comparison 2026
Sigil Pros and Cons
| Feature | Sigil | Snyk | Sonatype Nexus IQ | JFrog Xray | Checkmarx |
|---|---|---|---|---|---|
| Primary Function | Pre-execution code quarantine & behavior analysis | Post-install SCA & vulnerability management | Policy-driven SCA & repository firewall | Deep recursive scanning of binaries/artifacts | SAST & software supply chain security |
| Quarantine Focus | Intercepts git/npm/pip installs before execution | Scans after code is already installed/running | Scans at repository proxy (Nexus Repository) | Scans artifacts within the JFrog Platform | Scans code post-download/pre-build |
| AI/Behavior Focus | High (6-phase analysis for install hooks, obfuscation, exfil) | Low (focused on known CVEs in dependencies) | Medium (policy checks for license/security risks) | Medium (malware patterns, license compliance) | Medium (SAST patterns for malicious code) |
| Developer Workflow | CLI-first, replaces commands (e.g., sigil clone) |
IDE plugins, CLI, CI/CD integrations | Centralized policy management, CI/CD plugins | Integrated into JFrog Platform UI & CI/CD | Integrated into IDEs and CI/CD pipelines |
| Pricing Model | Free CLI; Pro $29/mo; Team $99/mo | Contact sales (enterprise-tier) | Contact sales (enterprise-tier) | Contact sales (enterprise-tier) | Contact sales (enterprise-tier) |
| Best For | Preventing malicious AI agent code from running | Finding known vulnerabilities in existing projects | Centralized governance of open-source usage | Security scanning within a JFrog ecosystem | Static analysis and broad AppSec testing |
Pros:
-
Pre-execution Blocking: Stops malicious code before it can execute, offering true quarantine.
-
Fast, Offline CLI: Scans locally in under 3 seconds with zero telemetry.
-
AI/Agent Focused: Specialized detection for AI tooling risks like MCP servers and hidden install hooks.
-
Open Core: Free Apache 2.0 CLI with transparent, auditable code.
-
Simple Integration: Easy alias for
git clone/npm installwith minimal configuration.
Cons:
-
Newer Ecosystem: Less brand recognition than established SCA giants.
-
Focused Scope: Primarily targets pre-execution quarantine, not a full SCA replacement.
Snyk Pros and Cons
Pros:
-
Extensive Vulnerability DB: Unmatched coverage for known CVEs across languages.
-
Developer Adoption: Excellent IDE integrations and developer experience.
-
Broad Platform: Includes SCA, SAST, container, and IaC security.
-
Strong Ecosystem: Wide range of CI/CD and platform integrations.
Cons:
-
Post-Execution Scanning: By the time Snyk finds an issue, the code may already be running.
-
Enterprise Pricing: Can be cost-prohibitive for smaller teams.
-
Misses Novel Threats: Relies on published CVEs, missing zero-day behaviors.
Sonatype Nexus IQ Pros and Cons
Pros:
-
Strong Policy Engine: Excellent for centralized governance and legal compliance.
-
Repository Firewall: Can block risky components at the Nexus repository proxy.
-
Accurate Data: High-quality vulnerability intelligence with low false positives.
Cons:
-
Proxy-Centric: Requires deployment and management of Nexus Repository Manager.
-
Complex Setup: Can be heavyweight for teams not already in the Sonatype ecosystem.
-
Limited Behavioral Analysis: Focuses on component attributes, not runtime behavior.
JFrog Xray Pros and Cons
Pros:
-
Deep Recursive Scanning: Unpacks and analyzes nested artifacts thoroughly.
-
Native JFrog Integration: Seamless for teams using Artifactory and the JFrog Platform.
-
CI/CD Native: Scanning is built into the pipeline within the platform.
Cons:
-
Vendor Lock-in: Most powerful when fully committed to the JFrog ecosystem.
-
Scanning Timing: Scans artifacts within the platform, which may occur after initial download.
Checkmarx Pros and Cons
Pros:
-
Strong SAST Foundation: Deep code analysis for custom source code.
-
Supply Chain Module: Extends SAST capabilities to open-source dependencies.
-
Enterprise-Ready: Scalable with extensive reporting and management features.
Cons:
-
SAST-Centric: Quarantine/pre-execution is not its primary design paradigm.
-
Scan Speed: Can be slower due to the depth of SAST analysis.
-
Complexity: May require significant security expertise to tune and manage effectively.
Which enterprise code quarantine solution should you choose?
The best choice depends on your primary security gap and existing toolchain.
Choose Sigil if: You need to stop AI agent and package threats before they execute, value a fast, local CLI for developers, and want to add a pre-execution quarantine layer in front of your existing SCA tools. It's ideal for AI-focused development shops and teams prioritizing zero-trust for third-party code.
Choose Snyk, Nexus IQ, or JFrog Xray if: Your primary need is governance and vulnerability management for code already in your systems, you are heavily invested in their respective ecosystems (GitHub, Nexus, Artifactory), and you have an enterprise budget for comprehensive SCA.
Choose Checkmarx if: Your focus is in-depth SAST and code analysis and you want supply chain security that extends from that core strength.
For a defense-in-depth strategy in 2026, the most effective approach is to layer Sigil's pre-execution quarantine with a robust SCA tool like Snyk. Sigil blocks the novel, behavioral threats at the door, while Snyk provides deep CVE analysis for the code that passes the initial checkpoint.
Designing a pre-execution quarantine workflow for CI/CD
An effective quarantine workflow integrates scanning directly into the developer and pipeline lifecycle. Here’s a practical design:
-
Developer Initiation: A developer runs
sigil cloneorsigil install. Sigil intercepts the command, downloads the code to a temporary, isolated location. -
Parallel Analysis: The tool runs its multi-phase scan (hooks, patterns, network, credentials, obfuscation, provenance) in under three seconds.
-
Policy Decision: Based on the risk score and organizational policy, the package is either:
-
Approved: Released to the developer's local environment or the CI workspace.
-
Quarantined/Blocked: The developer receives an immediate alert with the reason (e.g., "Blocked: contains obfuscated eval").
-
CI/CD Integration: In the pipeline (e.g., GitHub Actions), a Sigil step scans all pulled dependencies before the
npm ciorpip installstep executes. A failure blocks the pipeline. -
Audit & Enrichment: All scan results and decisions are logged. In Sigil Pro/Team, this data is synced to a cloud dashboard for historical analysis and can be enriched with threat intelligence feeds.
This workflow ensures no unknown code runs without inspection, creating a verifiable security gate. 2026 industry reports reveal that organizations are layering pre-execution code quarantine on top of SCA to meet regulatory and audit requirements for software bills of materials (SBOMs) and attestations.
How does Sigil complement existing SCA and security platforms?
Sigil is designed as a complementary force multiplier, not a replacement, for tools like Snyk, Nexus IQ, and Dependabot. It addresses the critical gap they leave open: the time between code download and execution.
-
SCA Tools Scan What's Installed: They excel at cataloging your dependencies and finding known vulnerabilities after the code is already on disk and potentially running.
-
Sigil Scans Before Anything Runs: It acts as a mandatory checkpoint, asking "should this code be allowed to run at all?" based on its behavior and provenance.
The combined value proposition is clear: Use Sigil to quarantine and block high-risk, behaviorally malicious packages at the point of download. Then, use Snyk to continuously monitor and alert on the approved codebase for newly discovered CVEs and license violations. Together, they cover the entire attack surface-from novel, pre-execution threats to known vulnerabilities in trusted code-providing a level of protection that typically requires multiple enterprise contracts.
What is an enterprise code quarantine solution and why do I need one?
An enterprise code quarantine solution is a security tool that intercepts and inspects code, packages, and artifacts before they are allowed to execute in your development or CI/CD environment. You need one to block malicious behaviors-like hidden install hooks, data exfiltration, or obfuscated malware-that traditional vulnerability scanners miss because they lack a CVE. It reduces risk by preventing threats from ever running on your systems.
How do code quarantine tools integrate with CI/CD pipelines and artifact repositories?
They integrate as dedicated security steps in your pipeline (e.g., a GitHub Action, GitLab CI job, or Jenkins plugin). The quarantine step executes immediately after code is checked out or before package installation commands run. If the scan fails, the pipeline is halted. For artifact repositories like Nexus or Artifactory, some tools can act as a repository firewall, scanning components as they are requested or uploaded.
Which enterprise products offer pre-execution quarantine for git, npm, and PyPI?
Sigil is specifically built for pre-execution quarantine of git clones, npm installs, and pip installs via its CLI that replaces those commands. Traditional SCA tools like Snyk and Nexus IQ primarily scan after installation. Some, like Nexus IQ's repository firewall, can block components at the proxy level, which is a form of pre-execution control for artifacts pulled from a managed repository.
How do Snyk, Nexus IQ, JFrog Xray, and Sigil compare for code quarantine and scanning?
Snyk, Nexus IQ, and JFrog Xray are primarily post-download scanning tools focused on known vulnerabilities, licenses, and policies. Sigil is a true pre-execution quarantine tool focused on behavioral threats. The key difference is timing: Sigil blocks code before it runs, while the others analyze code after it's already in your environment. They are best used together for defense-in-depth.
What should enterprises look for when evaluating code quarantine solutions in 2026?
Enterprises should prioritize solutions that: 1) Intercept commands at the developer CLI, 2) Perform fast, behavioral analysis (not just CVE matching), 3) Support air-gapped deployment, 4) Offer clear policy enforcement and audit trails, and 5) Integrate seamlessly into existing CI/CD pipelines and developer workflows without causing friction.
Key Takeaways
-
Pre-execution quarantine stops malicious code before it runs, while SCA scans code after installation.
-
Behavioral analysis in tools like Sigil catches threats without CVEs, such as hidden install hooks or obfuscated payloads.
-
The most robust 2026 strategy layers a pre-execution quarantine tool (e.g., Sigil) with a traditional SCA platform (e.g., Snyk).
-
Developer experience is critical; quarantine must be fast (seconds) and integrate directly into existing CLI workflows.
-
Air-gapped support and detailed audit logs are essential for regulated enterprises adopting code quarantine.
About the Author
Reece Frazier is the founder of NOMARK. He got tired of watching developers blindly clone repos with 12 GitHub stars and full access to their API keys, so he built Sigil.